
Industry
Protecting the Public Sector
Derisk Software and Files at Scale with On-Premises and Cloud-Managed Solutions and Seamless Integrations.
Federal agencies face relentless, evolving cyber threats that endanger sensitive data and national security. With vast, complex systems and millions of records, they remain top targets for cybercriminals and nation-state actors.
Resource constraints compound these risks, as many agencies operate with tight budgets, limited staff, and a shortage of skilled cybersecurity professionals. Furthermore, outdated tools and infrastructure widen security gaps, especially as the volume and complexity of files and software grow.
With a continued increase in software supply chain attacks that exploit third-party software to infiltrate government networks, defending the public sector is more challenging than ever.
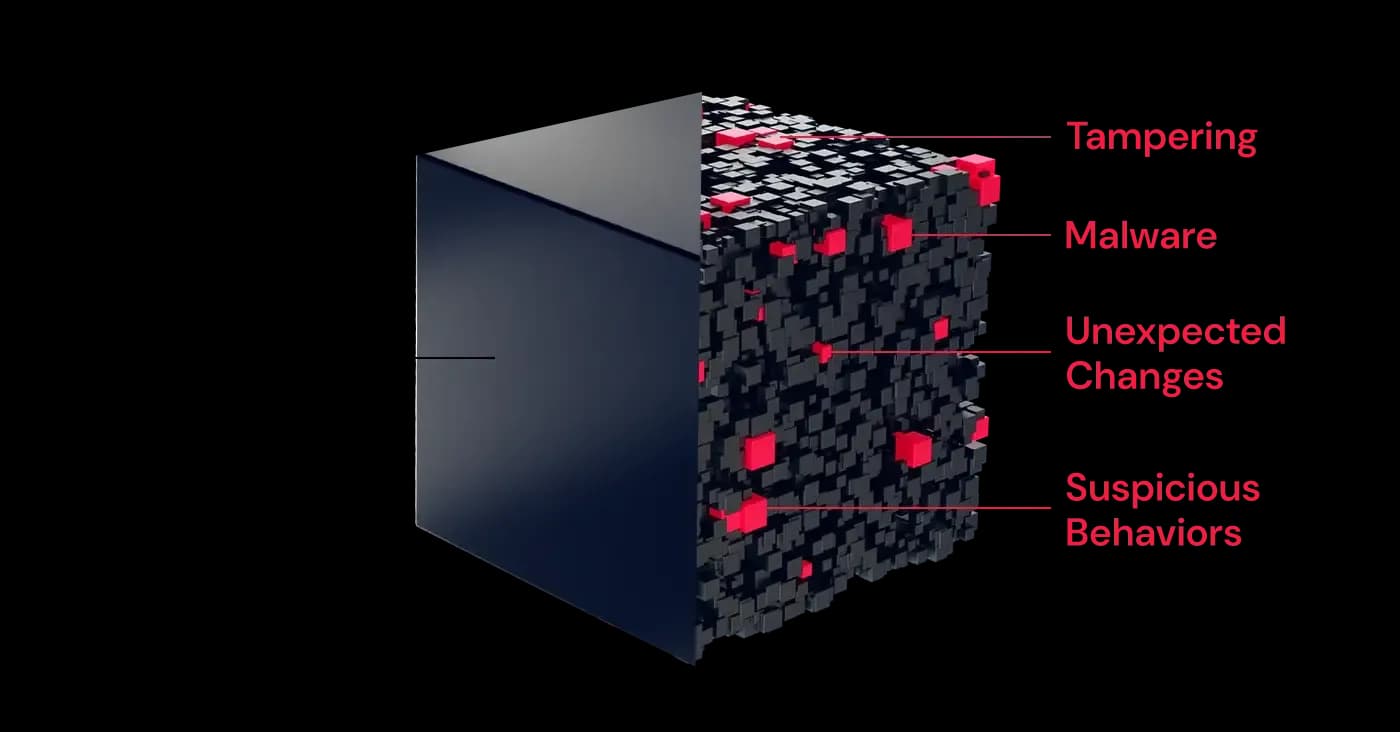
A common misperception is that legacy SAST and SCA tools are enough to secure the supply chain. They are not. Attacks on SolarWinds, 3CX, and Codecov were due to malware and tampering missed by those solutions. RL examines entire software binaries to detect embedded threats across software components, ML models, and artifacts - in minutes. Maintain pipeline velocity and stop malicious attacks.
Proprietary technology IP is a high-value target for ransomware. Tech-savvy employees are susceptible to phishing that leads to data theft. RL detects evasive and novel malware and ransomware that other tools miss. High-volume analysis of millions of digital assets per day from web traffic, email, endpoints, file shares, and cloud storage. Get attack protection without slowing existing workflows.
Ransomware poses a critical threat to public sector organizations, disrupting essential services and compromising sensitive data. With attacks increasing in frequency and sophistication, ReversingLabs provides the tools needed to detect and mitigate ransomware early. By leveraging the largest threat repository, advanced malware analysis, and industry leading software supply chain security (SSCS), organizations can prevent encryption, extortion, and operational downtime, safeguarding public trust.
Nation-state attacks pose a severe challenge to public sector organizations, targeting critical infrastructure and operational systems with advanced, persistent tactics. ReversingLabs helps counter these threats by identifying subtle software supply chain weaknesses beyond just vulnerabilities and detecting malicious activity at scale. By uncovering sophisticated techniques, such as tampering and malicious behaviors, ReversingLabs ensures resilient defenses against these highly strategic adversaries.
US:
European:
NASA SEWP V
NNG15SC03B/NNG15SC27B
May 01, 2015- Apr 30, 2025
ITES-SW2
W52P1J-20-D-0042
Aug 31, 2020- Aug 30, 2025
*Additional Option Years Available
Build Safe. Buy Safe. Stay Safe.
Spectra Assure® delivers the most comprehensive SBOM & risk assessment. Detect malware, tampering, and risks before you release or deploy commercial software.
Advanced Malware Analysis
An out-of-the box solution combining advanced static and dynamic analysis, real-time threat intelligence, plus powerful search and hunting - all from a single interface.
Illinois Public Higher Education Cooperative (IPHEC)
2011GAL
Jun 30, 2020- Apr 30, 2025
OH STS 0119Y
534354
May 31, 2012- Dec 19, 2026
RCA - Orange County - OMNIA Partners
RCA-017-21010004
May 01, 2021- Apr 30, 2025
Texas DIR-TSO-4288
DIR-TSO-4288
Feb 22, 2019- Feb 21, 2025
Cobb County, GA Technology Products, Solutions and Related Services - OMNIA Partners, Public Sector
23-6692-01
May 01, 2023- Apr 30, 2026
E&I Carahsoft Cloud Solutions & Services Distributor Contract
EI00063-2021MA
Apr 01, 2021- Mar 31, 2026
Educational Software Solutions and Services - OMNIA Partners, Public Sector
R191902
Feb 27, 2020- Apr 30, 2025
Golden State Technology Solutions Contract
CSBA-110822
Nov 08, 2022- Jul 01, 2025
Massachusetts Higher Education Consortium (MHEC)
MC15-04
Aug 10, 2019- Feb 28, 2025
NJSBA
E-8801-ACESCPS
Oct 20, 2015- Sep 03, 2025
The Quilt
MSA - 05012019F
Apr 01, 2016- May 02, 2028
VASCUPP
UVA1482501
May 02, 2014- Dec 19, 2026
Security at Scale
High-volume, high-speed inspection of files & objects for malware and threats, including web, email, endpoints, file shares, and cloud storage - scalable to millions of files per day.










-480x250.webp&w=1080&q=75)
Address the Full Scope of Software Risk from Malware to Tampering to AI to Crypto with Spectra Assure SAFE

Navigating the impact of CRA, NIS2, & DORA

As malware becomes more advanced, SOC teams need to reevaluate and evolve their approach to malware detection. Learn more in Modern Malware Analysis.