
Industry
Protect Your Software Supply Chains and Customers
Stop Malware, Tampering, and More Before You Ship or Deploy Any Software.
Technology providers remain high-value targets for malicious actors because their customers span many other industries, depending on commercial, third-party, and proprietary software to drive business value. As a result the threat landscape is constantly evolving.
The software supply chain – inclusive of software dependencies, production, delivery, acquisition, and deployment – represents the largest, under-addressed attack surface. Innovation to increase the pace of software creation and delivery has greatly outstripped the ability to provide comprehensive visibility into software components and embedded risks. Also missing are tools to provide in-depth review of software risk prior to purchase, and cannot scale to identify attacks embedded within software updates.
Malicious actors leverage these gaps to attack every software development and supply chain stage with increasingly subtle tactics.
The high tech industry requires more transparency to:

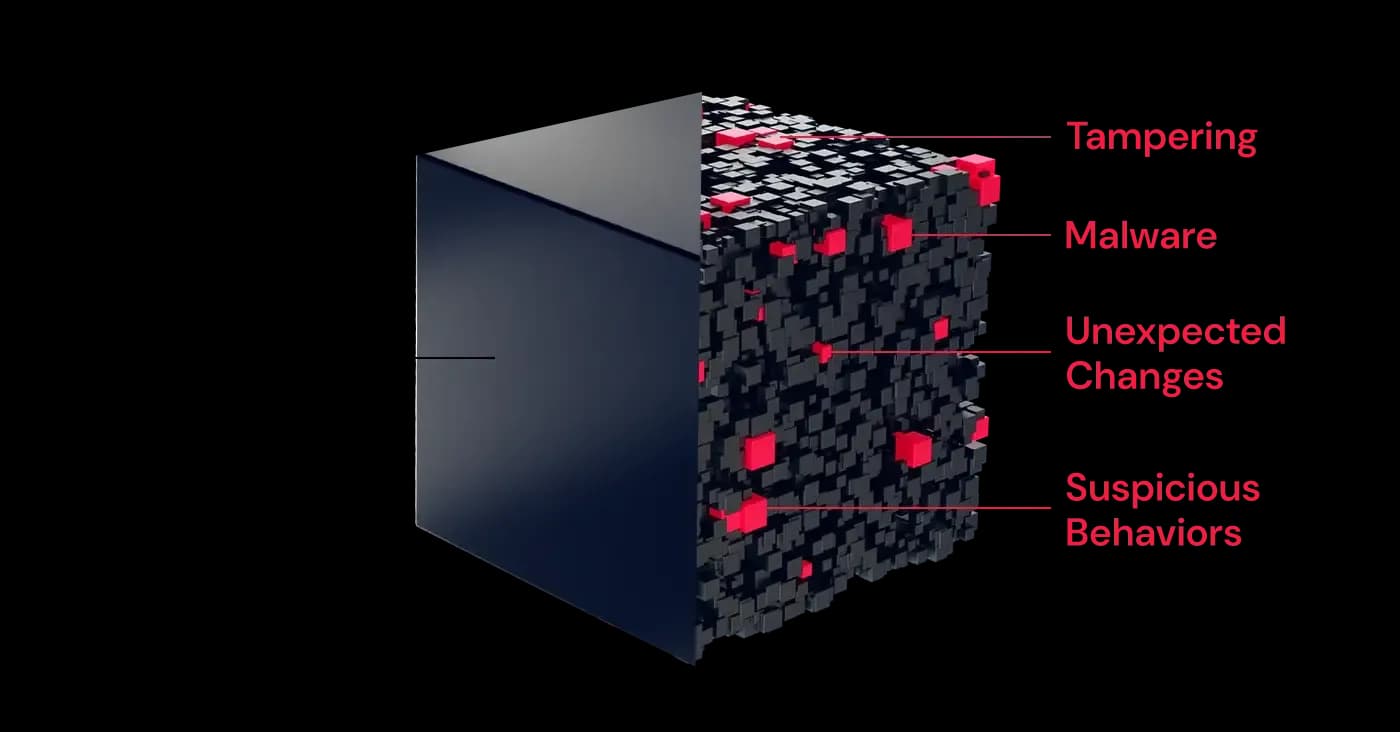
A common misperception is that legacy SAST and SCA tools are enough to secure the supply chain. They are not. Attacks on SolarWinds, 3CX, and Codecov were due to malware and tampering missed by those solutions. RL examines entire software binaries to detect embedded threats across software components, ML models, and artifacts - in minutes. Maintain pipeline velocity and stop malicious attacks.
.svg)
Proprietary technology IP is a high-value target for ransomware. Tech-savvy employees are susceptible to phishing that leads to data theft. RL detects evasive and novel malware and ransomware that other tools miss with high-volume analysis of millions of digital assets per day from web traffic, email, endpoints, file shares, and cloud storage. Get attack protection without slowing existing workflows.
Noisy detection tools make prioritization challenging for technology firms and triaging false positives wastes valuable time. RL cuts through noise using predictive threat models and intelligence curated from billions of files, so teams can focus on embedded malware, anomalous changes, and targeted attacks. Automated triage and threat-based prioritization improves remediation efficiency.
Security questionnaires and pentests cannot provide an in-depth risk analysis of commercial software prior to purchase, and cannot scale to identify attacks embedded in software updates. Spectra Assure® Complex Binary Analysis delivers a comprehensive assessment of commercial, freeware, and open-source software without the need for source code, closing the gap in vendor risk management.
EU’s DORA and CRA have stricter oversight and liability consequences for high tech. SEC fines demonstrate that both software builders and buyers need actionable risk insight. Spectra Assure provides the most comprehensive and flexible SBOM and risk reports before you ship or deploy. Share securely with internal stakeholders, customers, and regulators. Streamline compliance and attestation tasks.



Building a Path to Excellence in Software Supply Chain Security with Spectra Assure

Navigating the impact of CRA, NIS2, & DORA

Learn about complex binary analysis and how it tackles supply chain threats like malware, tampering, exposed secrets and more — all without source code.